Nested Virtualization for the KVM Backend for VirtualBox
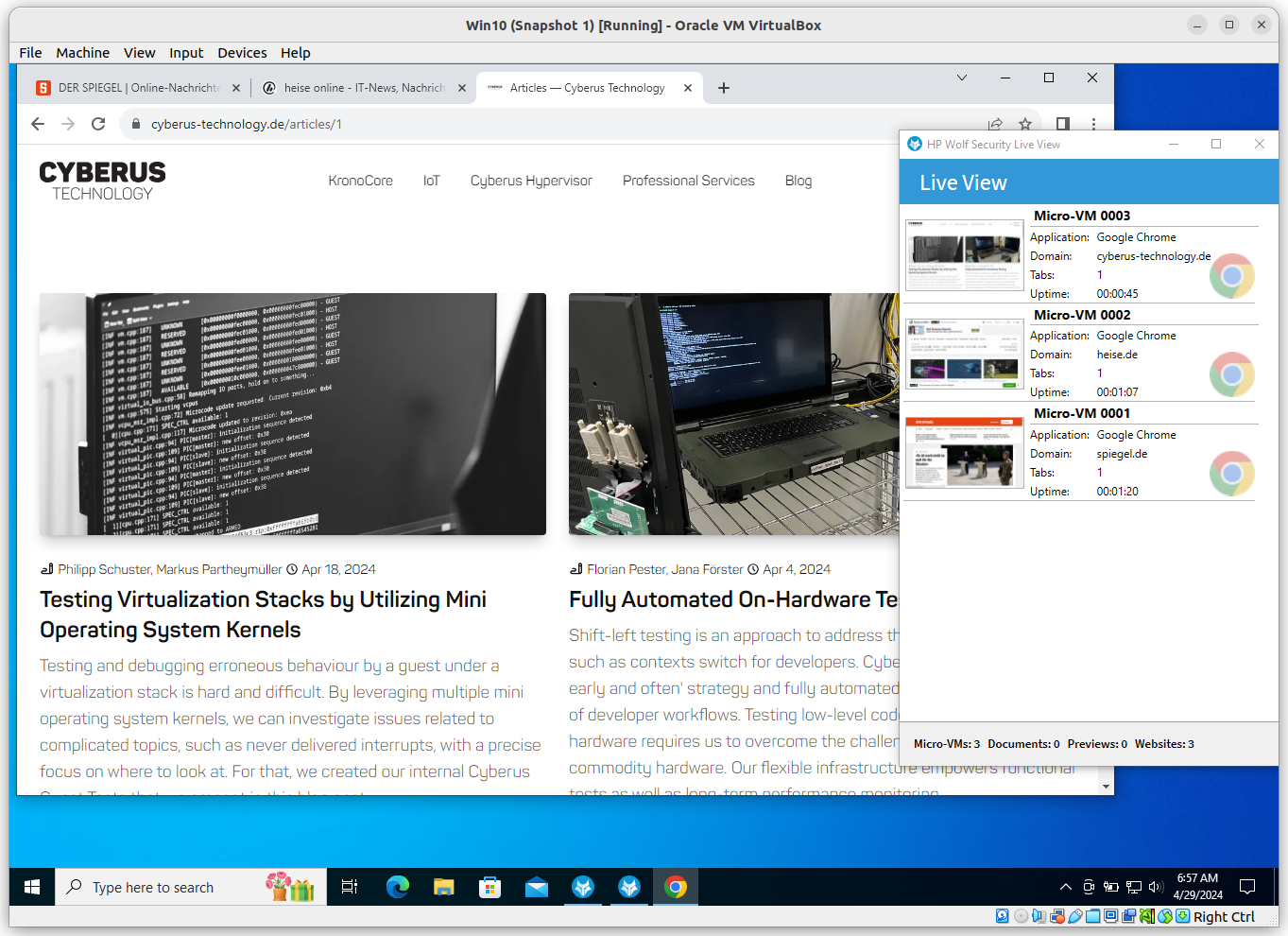
We're excited to share a new milestone for our KVM Backend for VirtualBox: nested virtualization is now supported. This means you can run virtual machines within other VMs, opening up new possibilities for testing and development environments. With nested virtualization, you can now run even more complex configurations, including HP Sure Click, enabling heightened security within virtualized environments.