Werner Haas · 4 min read
Cyberus Technology Presents new Perspectives on Virtual Machine Introspection at Biggest German IT Security Congress
Compromised software of the trusted compute base is a major challenge as it allows attackers to fly under the radar. VMI provides for defense-in-depth and enables event-driven response in a sandbox environment

The 17th German IT-Security Congress, organized by the Federal Office for Information Security (BSI), took place on February 2/3 and Cyberus Technology was among a select group of companies providing insights into new developments in this field. Given we are probably best known for our secure virtualization platform (SVP), we used the opportunity to highlight security-related use cases beyond virtualization’s isolation properties. Starting point were the recent Solarwinds-related security incidents that highlight the need for more checks and balances in current computer systems. How can we limit the consequences of compromised software, even when a trusted system component is affected? We presented Virtual Machine Introspection as game changing answer and talked about its basic principles in laymen’s terms. In the following you will find a condensed version of our talk.
Key Points:
- Compromised software of the trusted compute base is a major challenge as it allows attackers to fly under the radar
- VMI provides for defense-in-depth and enables event-driven response in a sandbox environment
- Our microkernel-based architecture offers fine-grained access rights managements, thus limiting the consequences of vulnerabilities
SolarWinds
Most of you surely heard about the supply chain attack via SolarWinds. It is particularly fiendish because SolarWinds itself is a trusted software provider in the IT infrastructure and the company even suggested excluding its files from standard anti virus checks. This contributed to attackers operating undetected for months in their victim’s environment. The SOHO image of a solar erruption provided the background for our proposition that we need an architecture with checks and balances, such that a compromised, privileged component does not jeopardize the entire system.
Virtualization
The origins of virtualization lay, of course, in resource utilization considerations. The strong isolation properties, however, that enable operating multiple virtual machines (VMs) in parallel, also provide means for protecting defender tools. Our high level architecture diagram shows how for example intrusion detection can be shielded and hidden from an attacker by moving it outside the VM it is meant to guard.
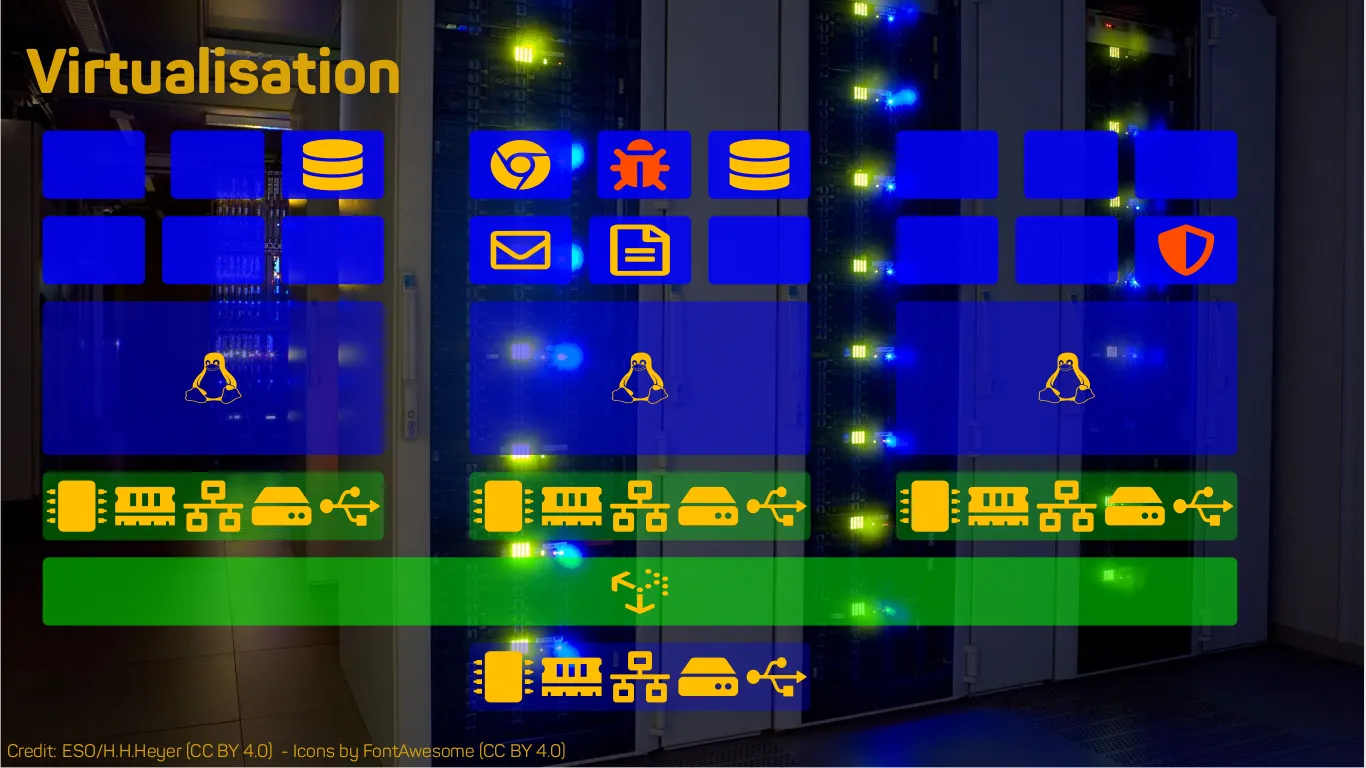
This works because access to the hardware state is at the discretion of the hypervisor layer. It can allow inspection of memory content or even CPU registers to other entities. There is a little caveat, however, because knowing the raw data values is insufficient for the discovery of abnormal behaviour. One also needs context information and we briefly touched upon the semantic gap problem, a recurring term at this year’s congress. More details on how we enable Windows analysis in a generic manner can be found in the proceedings. You can access them via the information desk at the congress’ web site.
Isolation and inspection capabilities already provide a solid foundation for security tool development. This led, for example, to sandboxing solutions in order to evaluate email attachments. There is yet another ‘I’, though, the so-called interposition. The hypervisor sits between the virtual hardware (that the legacy software stack operates on) and the real thing, much like the moon sits on the line of sight to the sun in case of a solar eclipse. Thus the hypervisor controls the interaction with the hardware which enables reactive behavior. Even relatively dumb activities like a straight forward memory analysis using YARA rules can be simplified as it can operate directly in virtual address space instead of stitching together physical memory dumps and Windows pagefile content. Once more you can find further ideas on how to use interposition in our paper.
Virtual Machine Introspection
With our talk we wanted to shed some light on the enormous potential of Virtual Machine Introspection for improving system security. Of course, it should be paired with an appropriate hypervisor architecture. This combination allows the implementation of the checks and balances mentioned in the introduction.
Further Information
If you are interested in learning more, the congress’ web site, with a recorded version of our talk (in german, though) shall be accessible for another month. From there you can also download the proceedings with our paper (in english). Of course, feel free to contact me directly if you have further questions or want to learn more about Cyberus Technology’s vision with respect to VMI and IT security.